Phishing Attacks: Basic Detection and Prevention
What is Phishing?#
Phishing can be described as an attempt to steal information from victims through the use of social engineering techniques (pretexting) and various communication channels such as through email and over the phone.
Phishing is a form of cyberattack where attackers use fraudulent communication, often disguised as legitimate entities, to trick individuals into providing sensitive information such as passwords, credit card numbers, or personal details. There are various types of phishing attacks, each with its own tactics and targets. Some common types include:
Email Phishing: This is the most prevalent form of phishing. Attackers send deceptive emails pretending to be from legitimate sources, such as banks, government agencies, or well-known companies. These emails typically contain links to fake websites or malicious attachments designed to steal sensitive information.
Spear Phishing: Unlike regular phishing attacks, spear phishing is highly targeted and personalized. Attackers gather information about specific individuals or organizations to craft emails that appear more convincing. They may use the target’s name, position, or other relevant details to increase the likelihood of success.
Whaling: This is a specialized form of phishing that targets high-profile individuals within an organization, such as executives or CEOs. The goal is to steal sensitive corporate information or gain access to valuable accounts by tricking these individuals into revealing their credentials or other confidential data.
Vishing (Voice Phishing): Vishing involves using phone calls or voice messages to deceive individuals into providing personal information or financial details. Attackers may spoof caller IDs to make the calls appear legitimate, such as pretending to be from a bank or government agency.
Smishing (SMS Phishing): Similar to email phishing, smishing uses text messages instead of emails to trick recipients into divulging sensitive information or clicking on malicious links. These messages often contain urgent requests or enticing offers to prompt immediate action.
Clone Phishing: In clone phishing attacks, attackers create fraudulent copies of legitimate emails that recipients have already received and interacted with. These copies, which may contain malicious links or attachments, are designed to appear identical to the original messages, increasing the likelihood of success.
Search Engine Phishing: In this type of attack, scammers manipulate search engine results to promote fake websites designed to steal sensitive information. Victims searching for legitimate services or information may inadvertently click on malicious links, leading them to phishing pages.
Domain Spoofing: Domain spoofing involves creating fake websites or email domains that closely resemble legitimate ones. Attackers use these spoofed domains to trick users into believing they are interacting with trusted entities, increasing the likelihood of successful phishing attempts.
Man-in-the-Middle (MitM) Phishing: In MitM attacks, hackers intercept communication between users and legitimate websites or services. By eavesdropping on the interaction, attackers can steal sensitive information such as login credentials or financial details.
Social Media Phishing: With the widespread use of social media platforms, attackers exploit these channels to launch phishing attacks. They may create fake profiles or pages impersonating trusted entities to trick users into disclosing personal information or clicking on malicious links.
These are just some of the common types of phishing attacks, and attackers continuously develop new techniques to evade detection and exploit vulnerabilities. Staying vigilant and adopting cybersecurity best practices are essential for protecting against phishing threats.
Motivations for phishing#
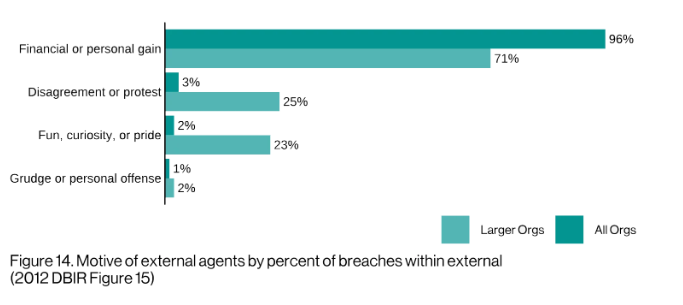
According to the 2022 Verizon Data Breach Investigations Report, 96% of all organizations in the study were targeted due to financial motivation by the malicious hacker.
The report also states that:
“Web Applications and Email are the top two vectors for breaches. This is followed by Carelessness, which is associated with Errors such as Misdelivery and Misconfiguration.”
This post will mainly center around phishing detection and prevention from a threat actor who is motivated towards identity, credential and/or financial theft.
The bait#
A successful phishing attempts requires an attacker to establish trust through building credibility with the victim.
One example of an attack requiring victim trust is a lateral phishing attack.
Lateral phishing attack (Business Email Compromise)#
A phishing email is sent from a legitimate, but compromised company email account would trick other employees to click on links sent by the malicious actor because there is established trust that this is a person they work with.
In 2019, the FBI estimated that business email compromise (BEC) scams alone have caused more than $26 billion in losses to businesses worldwide over three years from June 2016 to July 2019.
What happens when the user takes the bait? Is there a suspicious or malformed URL? How is the phishing email crafted?
Rapid7 has an excellent example https://www.rapid7.com/globalassets/_pdfs/infographics/rapid7_phishing_poster.pdf
What to look for:
- Is there a different
Reply ToandFromaddress? - There’s a contact name, email or company you don’t do business with
- Unusual level of urgency: deadlines, exclamation marks and text in all caps
- Spelling errors and clumsy wording
- Suspicious or unexpected attachments
- Requests for personal or confidential information
- Found to be a malformed URL when hovered over
People are easily compromised and preparing your employees to understand social engineering techniques comes down to user training, a well trained userbase is your best defense against phishing.
Awareness and Training#
Rapid7 has a great article on phishing training and awareness. User awareness and training on phishing attacks can lead to user reporting of phishing emails to IT and security staff. Employee training can involve simulated phishing campaigns by your company’s security team.
When an employee clicks on the fake phishing email, reinforce the phishing awareness training by showing them a video and quiz them based on the information in the video.
Analyze the results of the phishing training:
- What attacks were the most successful?
- Which departments/teams were the most vulnerable?
- How can the training be improved?
Detecting Comprimised Users#
One solution to securing your email and generally your Office 365 ecosystem is
using Microsoft’s Defender for Office 365.
Microsoft offers a couple different plans that may be affordable for a small business.
Plan 1 is $2.00/user/month and offers:
- Protection against advanced cyberattacks, such as phishing, malware, spam, and business email compromise
- Protection beyond email (Microsoft Teams, SharePoint, OneDrive, and Productivity apps)
- Internal email protection
- Detailed reporting
Plan 2 is $5/user/month and offers:
- Protection against advanced cyberattacks, such as phishing, malware, spam, and business email compromise
- Protection beyond email (Microsoft Teams, SharePoint, OneDrive, and Productivity apps)
- Internal email protection
- Detailed reporting
- Advanced cyberthreat hunting
- Automated investigation and response
- Cyberattack simulation training
- Microsoft Defender XDR capabilities, such as cross-domain hunting and incident correlation
Details above sourced from: https://www.microsoft.com/en-us/security/business/siem-and-xdr/microsoft-defender-office-365
Security Information and Event Management (SIEM) technology is also helpful for network-wide visibility to detect a user’s post-compromise attack path. Unfortunately SIEMs are time consuming and expensive to setup and require a trained cybersecurity team to monitor for alerts and maintenance.
Phishing Prevention / Mitigation#
- Proactively block phishing email hosting domains with IP blacklists.
- Proactively block phishing email with products such as Microsoft Defender for Office 365.
- Detect comprimised users and have a plan to act.
- Limiting you or your company’s OSINT footprint to minimize a malicious hacker’s ability to craft a credible phishing email.
- Email providers with two-factor authentication.
- Email provider with end-to-end encryption.
- Cloud email security products with ability to filter emails and detect malicious URLS + attachments.
- User Awareness and Training - teaching users to look at message content, request type, hovering over URLs, knowing when to contact the sender’s phone no. found on their official company website, etc.
- Implement DMARC (prevents unauthorized communication from your domain)
- If your company uses Office 365 then this article is a guide on setting up DMARC records for your email domain.
If you found this article helpful and want to support me in my content creation then buy me a coffee